US Army Data Breach: 70,000+ Files Exposed for Over a Year Despite CISA Alert
A critical security lapse left more than 70,000 U.S. Army files—including sensitive personnel records, contractor details, and base schematics—exposed to the public for over a year. The data was stored in an Open Directory Listing, a misconfiguration that allows anyone to browse files without authentication. Even after the Cybersecurity and Infrastructure Security Agency (CISA) issued a warning, the vulnerable directory remained open. This incident highlights the persistent risks of misconfigured storage systems in military environments. Below, we answer key questions about the breach, its impact, and what went wrong.
What exactly was the U.S. Army data exposure?
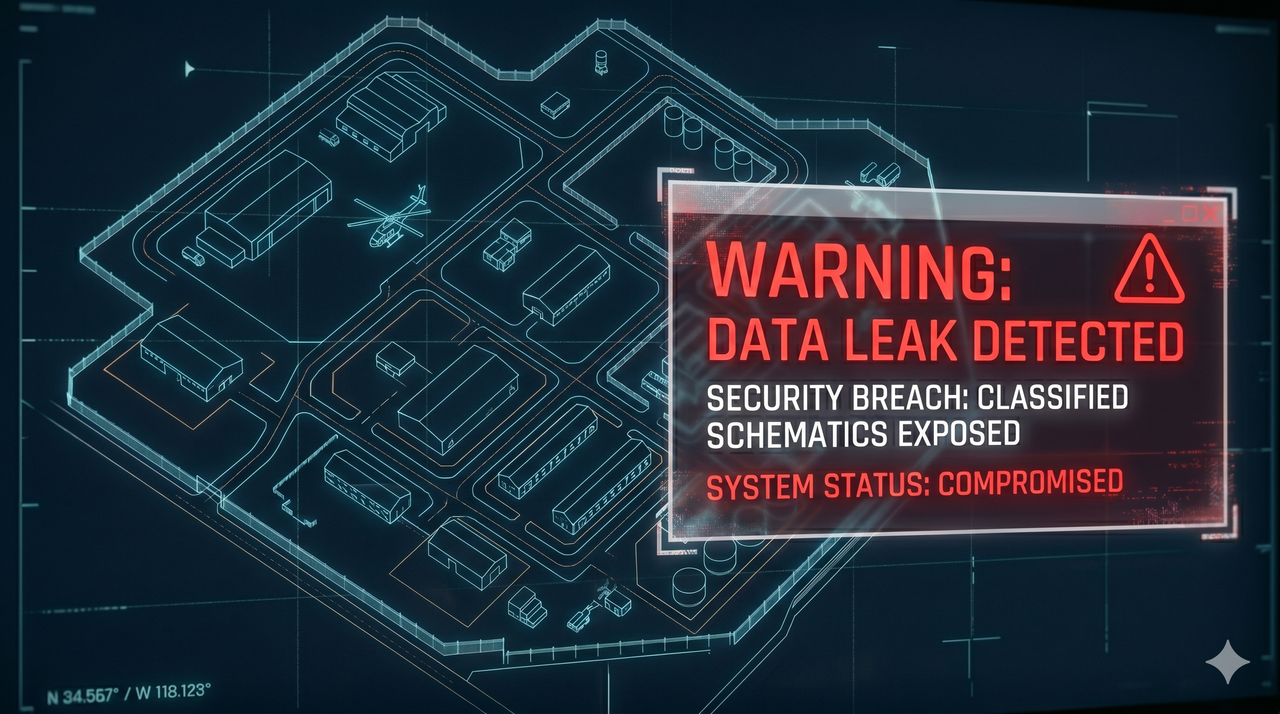
Between 2022 and 2023, a publicly accessible Open Directory Listing exposed more than 70,000 files from the U.S. Army. The directory was misconfigured, meaning no password or encryption was required to view or download the contents. Among the exposed files were personally identifiable information (PII) of soldiers and civilian employees, names and contact details of contractors, and detailed schematics of military bases. The data remained accessible for over a year, even after CISA notified the Army. The directory was eventually taken down, but not before potential adversaries could have harvested the information.
What sensitive information was contained in the exposed files?
The exposed files included a wide range of sensitive material. Personnel records contained full names, Social Security numbers, dates of birth, and security clearance levels of U.S. Army service members and civilian staff. Contractor data included company names, project details, and individual contact information. Most alarmingly, the repository held base schematics—floor plans, utility layouts, access points, and structural details of military installations. Such blueprints could be used to plan physical intrusions or attacks. Additionally, some files contained operational procedures and internal communications that would aid adversaries in understanding Army protocols.
Why is an Open Directory Listing considered a high-risk vulnerability?
An Open Directory Listing occurs when a web server is configured to allow anyone to browse its file system without authentication. Unlike a password-protected portal, anyone with the URL can view, download, or index the files. For the Army, this meant that even routine web searches or scanning tools could discover the directory. Once accessed, an attacker could aggregate personal data for identity theft, use base schematics for espionage, or analyze contractor relationships for supply-chain attacks. The lack of encryption also meant data in transit was visible. Because no credentials are required, the exposure is often widespread and difficult to detect until a third party reports it.
Was CISA's warning about the breach ignored?
According to security researchers who discovered the exposure, CISA was notified early in the incident and promptly alerted the Army. However, the Open Directory Listing remained accessible for more than a year after that notification. This suggests that either the Army did not prioritize the fix, or the responsible administrators did not act swiftly. The delay is concerning because CISA typically provides guidance and threat intelligence to federal agencies. The continued exposure implies a breakdown in the reporting and remediation process within the military's IT security chain. Researchers eventually took down the directory by contacting other officials after the initial warning failed to produce action.
What are the potential consequences of this data exposure?
The fallout from the exposed Army files is severe. For individuals, leaked PII increases the risk of identity theft, phishing attacks, and social engineering—especially against military personnel and their families. For national security, the base schematics could allow foreign intelligence services or terrorist groups to map out vulnerabilities in physical infrastructure. Contractors may face reputational damage and loss of trust if their sensitive business data is misused. Moreover, the prolonged exposure period means any adversary with access to the internet could have downloaded and analyzed the files. The incident also undermines public confidence in the Army's ability to safeguard classified and controlled unclassified information.
What lessons can be learned from this breach?
This case underscores several critical lessons. First, automated asset discovery and configuration management are essential to catch misconfigured directories before they are exploited. Second, security alerts from agencies like CISA must be treated with the highest priority, especially when they involve military data. Third, the human element—administrators failing to apply patches or follow up on warnings—remains a weak link. Fourth, organizations should implement defense-in-depth measures, such as requiring authentication for any directory containing sensitive files, even internal ones. Finally, periodic third-party audits can help identify exposures that internal teams might overlook. Without these practices, similar breaches will continue to occur.
What immediate steps should the U.S. Army take after this incident?
To prevent future exposures, the Army should conduct an inventory of all Open Directory Listings within its networks and enforce a policy requiring authentication for any folder containing PII or operational data. Affected individuals—soldiers, civilians, and contractors—should be notified and offered credit monitoring services. Base schematics must be reclassified and stored in encrypted, access-controlled repositories. The Army should also review its incident response workflow to ensure CISA warnings are escalated and addressed within a strict timeline. Finally, leadership should invest in continuous security training for IT staff to emphasize the dangers of misconfigurations. Accountability for the year-long delay must be established to reinforce the seriousness of data protection.
Related Articles
- 10 Things You Need to Know About the reMarkable Paper Pure
- Vitest 4.1: Enhanced JavaScript Testing with Tags, Experimental Mode, and More
- Salesforce Invests in 1,000 AI-Savvy New Graduates and Interns
- Ubuntu 26.04 LTS 'Resolute Raccoon' Goes Live: A Two-Year Leap in Performance and Security
- OpenTelemetry Adoption Surges as Developers Seek Deeper Observability Beyond Logging
- Elle Prequel Series: Everything You Need to Know About the Legally Blonde Spin-Off
- The Agentic Cloud Revolution: Your Questions Answered on Cloudflare’s Latest Innovations
- Pixel Perks: Ranking Google's Top Exclusive Features